Anthropic restricts AI access: 99% of vulnerabilities are unpatched, 40 major firms join forces for defense
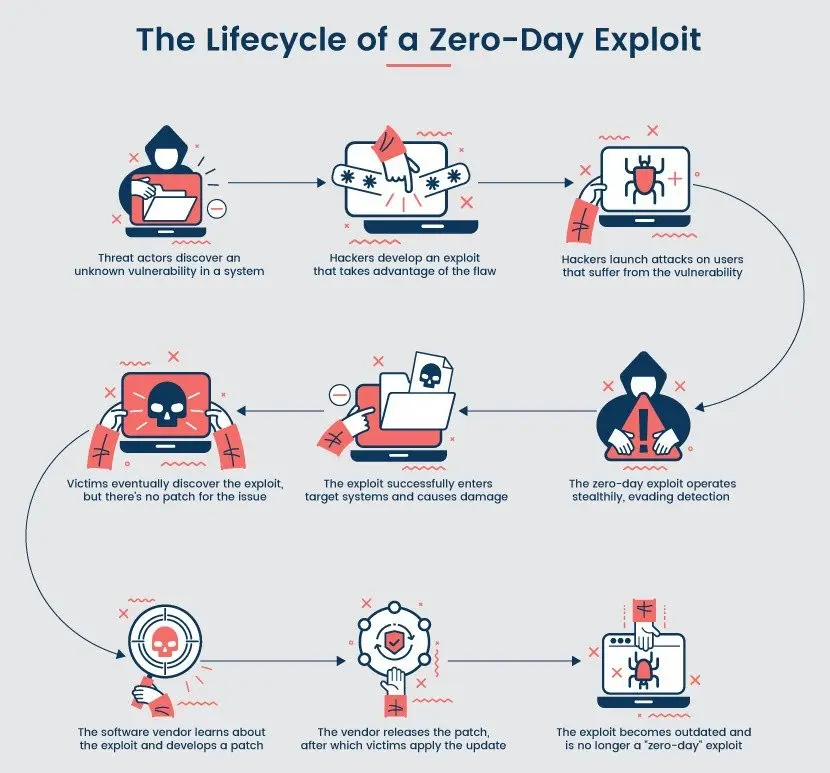
Anthropic announced that its new general-purpose AI model, Claude Mythos Preview, has been found with thousands of critical vulnerabilities across mainstream operating systems, web browsers, and cryptographic protocols, with 99% of them still unpatched. Given that malicious actors can exploit this capability, Anthropic is providing it only to select partner organizations, and has simultaneously launched the “Glasswing Project,” involving 40 or more institutions in a joint effort.
Discoveries in Claude Mythos Preview: From 27-Year-Old Vulnerabilities to Crypto Protocol Weaknesses
 (Source: PhoenixNAP)
(Source: PhoenixNAP)
The scope and depth of the vulnerabilities scanned by Claude Mythos Preview far exceed industry expectations. Anthropic said these vulnerabilities are “typically very subtle or difficult to detect,” and most have been lurking in systems for decades, with severe security flaws present in all major software, including all mainstream operating systems and web browsers.
Specific findings include: a vulnerability in OpenBSD that had been lying dormant for 27 years (already fixed), making it the oldest vulnerability discovered so far; a 16-year-old flaw in the FFmpeg media processing library; a 17-year-old remote code execution vulnerability in the FreeBSD operating system; and numerous vulnerabilities in the Linux kernel. The most widely used global cryptographic libraries and protocols were also not spared—weaknesses were found in TLS, AES-GCM, and SSH. For web applications, the vulnerabilities cover common attack vectors such as cross-site scripting (XSS), SQL injection, and cross-site request forgery (CSRF).
Because 99% of the discovered vulnerabilities remain unpatched, Anthropic explicitly stated that it will not disclose the details of these vulnerabilities: “If we disclosed details about these vulnerabilities, that would be irresponsible.”
Glasswing Project: A Proactive Defense Network Involving 40+ Tech and Finance Giants
On Tuesday, Anthropic announced the launch of the “Glasswing Project,” applying Claude Mythos Preview’s vulnerability-discovery capabilities for defensive purposes—completing patches before malicious actors can exploit them—and sharing vulnerability data among partner organizations to enable coordinated defense.
Key Participating Organizations in the Glasswing Project
· Amazon Web Services
· Apple
· Cisco
· JPMorgan Chase
· Linux Foundation
· Microsoft
· NVIDIA
(40+ institutions in total)
The rationale behind launching this initiative is that the number of AI-driven cyberattacks is growing at a year-over-year rate of 72%. By 2025, Anthropic expects 87% of organizations worldwide will face AI-driven cyberattacks, and believes that proactively leveraging AI is currently the most systematic response option.
Long-Term Outlook: Defensive Capabilities Will Eventually Take the Lead, But the Transition Period Is Full of Challenges
Anthropic emphasized that “protecting the world’s network infrastructure may take years,” but it remains cautiously optimistic about the long-term outlook, expecting that “defensive capabilities will take the lead: the world will become safer, and software will become more robust—largely thanks to the code written by these models. But the transition period will be full of challenges.”
Anthropic also warned that “given the speed of AI development, this capability will spread quickly and may go beyond the control of those participants who are focused on deploying it for security,” which is also the core logic behind limiting access to Claude Mythos Preview.
Frequently Asked Questions
Why does Anthropic restrict access to Claude Mythos Preview?
Claude Mythos Preview already has the capability to surpass the vast majority of humans in discovering and exploiting software vulnerabilities. Anthropic is concerned that if this capability spreads broadly, malicious actors could use it for large-scale cyberattacks. For this reason, Anthropic decided to provide the model only to selected partners to ensure that its capabilities are applied within a controllable scope.
What is the Glasswing Project (Project Glasswing)?
The Glasswing Project is Anthropic-led defensive AI security initiative. It brings together 40+ technology and financial institutions to actively scan partner systems for security vulnerabilities using Claude Mythos Preview, complete patches before attackers can exploit them, and share vulnerability data among partner organizations to enable systematic coordinated defense.
Have the vulnerabilities discovered by Claude Mythos Preview been publicly disclosed?
Anthropic said that among the currently discovered vulnerabilities, 99% remain unpatched. Therefore, the company has clearly stated that it will not publish the specific details of the vulnerabilities, to avoid providing attack paths to malicious attackers. Patched cases include a vulnerability in OpenBSD that had been dormant for 27 years.