How Do Dfinity Applications Run? A Full Walkthrough from Deployment to Execution
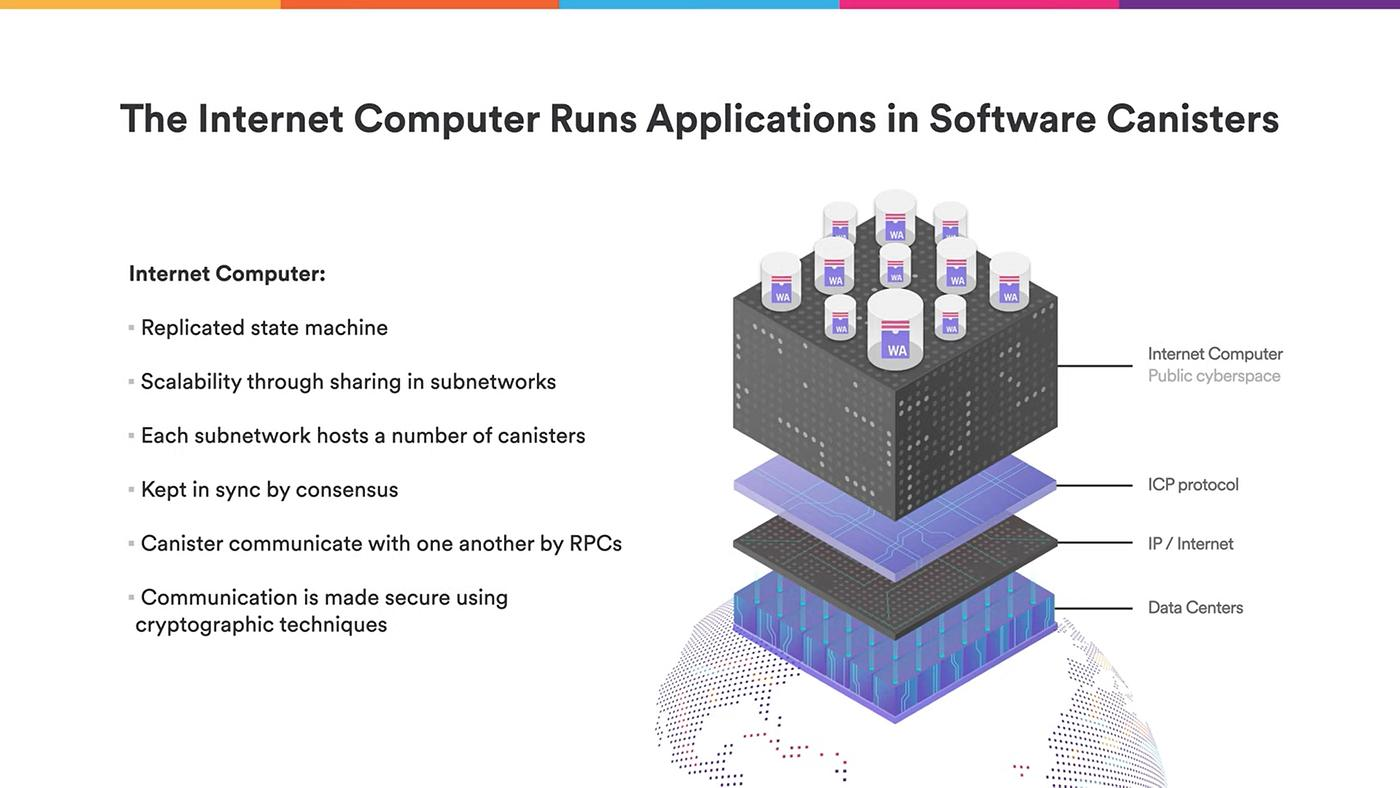
In traditional application architectures, developers typically rely on servers to process requests. In contrast, within the Internet Computer network, application logic runs directly on blockchain. This shift often leads to confusion when trying to understand how these applications operate.
At its core, this involves three layers: application architecture, request execution, and consensus verification. Together, they form the complete lifecycle of a Dfinity application, from deployment to execution.
How Dfinity Application Architecture Differs from Traditional Web Apps
Dfinity applications use an on-chain computing architecture, which differs significantly from traditional web applications.
Mechanically, traditional apps rely on a layered structure of frontend, backend, and database. Dfinity consolidates these functions into Canisters, where both application logic and data run directly on-chain.
Structurally, a Dfinity application consists of a frontend interface and multiple Canisters. Each Canister handles both business logic and data storage, reducing reliance on centralized servers.
The significance of this design lies in enabling applications to operate in a decentralized way while still maintaining full functionality.
Developers deploy Canisters to upload application logic to the network.
From a process standpoint, developers write code, compile it into a Canister, and deploy it to a specific subnet using dedicated tools. This deployment consumes Cycles as a form of computational resource.
Structurally, deployment involves three steps: code packaging, resource allocation, and subnet registration. Once deployed, a Canister is immediately capable of receiving user requests.
This step marks the transition of an application from a local environment into an on-chain executable entity.
How Canisters Handle Data Storage and Request Processing
Canisters are the core units responsible for running applications within Dfinity.
Mechanically, each Canister contains both code and state. It can process user requests, perform computations, and update stored data. It functions as both an execution engine and a persistent storage layer.
Structurally, each Canister operates like an independent service unit. Multiple Canisters can interact with one another to form a complete application system.
This design gives blockchain-based systems capabilities similar to traditional backend services.
How User Requests Are Executed Within ICP Subnets
User requests are executed and processed within subnets.
Mechanically, a request is first routed to the subnet where the target Canister resides. Nodes within that subnet collectively execute the request and generate a result.
Structurally, a subnet is composed of multiple nodes that work together to process requests and maintain a consistent state. The execution result is then returned to the user.
This ensures that request processing occurs in a decentralized environment while maintaining consistency.
How the Dfinity Consensus Mechanism Ensures Consistent Results
The consensus mechanism ensures that all nodes agree on execution outcomes.
Mechanically, nodes synchronize state and validate computation results through a consensus protocol, preventing forks or inconsistencies.
Structurally, the consensus system connects nodes within a subnet, keeping them aligned throughout execution.
This mechanism enables reliable computation in a distributed environment.
How Canister Upgrades and Application Maintenance Work
Canisters support upgrades and ongoing maintenance.
Mechanically, developers can update Canister code while preserving its existing state. This avoids data loss during upgrades.
Structurally, the upgrade process involves coordination between deployment modules and state management systems, allowing applications to evolve over time.
This design ensures that on-chain applications can be maintained long term.
Execution Flow and Request Lifecycle of On-Chain Applications
The operation of a Dfinity application can be broken down into a series of steps:
Step 1: Canister Deployment Developers deploy application logic as Canisters and allocate computational resources.
Step 2: User Request Initiation Users send requests to Canisters through the frontend interface.
Step 3: Request Routing to Subnet The request is routed to the appropriate subnet and queued for processing.
Step 4: Node Execution Nodes within the subnet execute the Canister code and update state.
Step 5: Consensus Confirmation Nodes reach agreement on the execution result through the consensus mechanism.
Step 6: Response Return The final result is returned to the user, completing the interaction.
Mechanically, this process is powered by coordination between Canisters, subnets, and the consensus system.
Structurally, each step is handled by a distinct component, creating a clear and traceable execution path.
This workflow transforms user requests into verifiable on-chain computations.
Summary
Dfinity applications rely on Canisters, subnets, and consensus mechanisms to form a complete runtime system, enabling deployment, execution, and maintenance entirely on-chain.
FAQ
What is a Canister?
It is a smart contract-like unit in Dfinity used to run application logic.
Do applications have to run within subnets?
Yes, execution is carried out collectively by subnet nodes.
How are user requests processed?
They are executed by Canisters and verified through consensus.
Can Canisters be upgraded?
Yes, and they support preserving existing data during upgrades.
What is the biggest difference between Dfinity apps and traditional apps?
Application logic and data run directly on the blockchain.
Related Articles

The Future of Cross-Chain Bridges: Full-Chain Interoperability Becomes Inevitable, Liquidity Bridges Will Decline

Solana Need L2s And Appchains?

Sui: How are users leveraging its speed, security, & scalability?

Navigating the Zero Knowledge Landscape

What is Tronscan and How Can You Use it in 2025?


